Infosec
CrowdStrike Update Causes Global Microsoft Outages: What You Need to Know
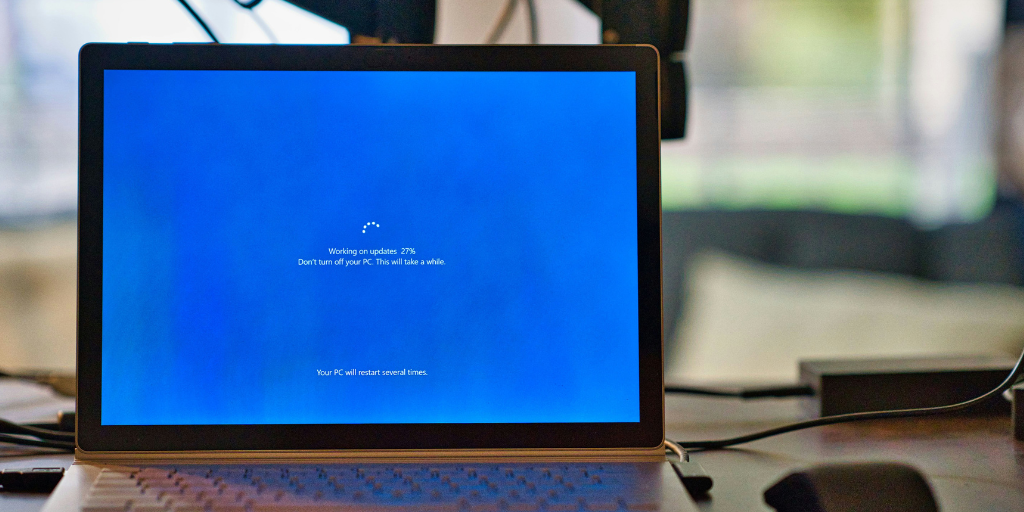
On the morning of July 19, millions woke to the news that businesses across the world were impacted by a global computer outage caused by a bug in an update to cybersecurity software CrowdStrike.
July 19, 2024
Read More

Watch on Demand: Strengthening Remote Access in Healthcare with Zero Trust
Recently, OpenVPN hosted a webinar for those in the healthcare industry to learn more about how zero trust can keep their patient data safe. If you missed the webinar, you can still catch the replay here. Network Security Challenges in Healthcare Healthcare organizations, especially those with remote employees or providers who travel between multiple sites, […]
June 12, 2024
Read More

How The Great Resignation Weakened Network Security (and What You Can Do About It)
As the Great Resignation reshapes the workforce, organizations must confront the challenges it presents for cybersecurity. The departure of cybersecurity talent and the intensification of cyber threats demand immediate action. By cultivating a cybersecurity-focused culture, investing in upskilling, leveraging managed security services, and enhancing insider threat mitigation, businesses can navigate the uncharted waters of talent and risk.
March 27, 2024
Read More

Navigating Cybersecurity: Choosing Between All-In-One Platforms and Point Solutions
The cybersecurity industry, and SaaS as a whole, is continually reshaping and changing through acquisitions. These deals have led to a boom in consolidated platforms offering multiple bundled solutions, and more companies attempting to satisfy multiple use cases through a diverse product portfolio. However, these all-in-one platforms come with a cost (literally and figuratively). IT […]
December 15, 2023
Read More

Minimize Your Attack Surface with CloudConnexa® Device Identity Verification & Enforcement (DIVE)
Cloud Connexa Device Identity Verification & Enforcement (DIVE) gives administrators the power to leverage one of the key principles of Zero Trust Network Access (ZTNA) — Least Privilege — granting access to only the resources a user should have, from only the devices they are authorized to use. When combined with the inherent Cloud Connexa micro-segmentation and identity-based access controls, DIVE further minimizes the attack surface.
April 18, 2023
Read More

Three Ways to Integrate Device Posture Checks With Your VPN
In today's increasingly mobile and BYOD workforce, ensuring employees use secure devices when connecting to corporate networks is more critical than ever. Device posture information can help you identify and mitigate security risks in your business by ensuring that devices are updated with security patches, have antivirus software installed, and are not jailbroken or rooted.
April 4, 2023
Read More

Anonymity, Privacy, and Security
Often, when I'm involved in discussions on various forums and discussion threads related to security and privacy on the Internet, I'm surprised how many people use the terms “anonymity,” “privacy,” and “security” interchangeably. These are actually three very different ideas, although they do have some overlapping aspects. Let's dive into the definition of each word to see how they differ.
March 28, 2023
Read More

ZTNA — Beyond the Acronym
The traditional methods of ensuring secure communications across your organization can be overly complex and expensive for a myriad of reasons. ZTNA (Zero Trust Network Access) reduces the surface area prone to attack by following zero trust tenets to provide access to applications.
September 20, 2022
Read More

SOX Cybersecurity Compliance
The Sarbanes-Oxley Act (SOX) is a federal act passed in 2002 following financial scandals at Enron Corp., Tyco International, and WorldCom. Here's what you need to know.
June 16, 2022
Read More

What is LDAP?
In 1993, LDAP was introduced, allowing applications to access and authenticate specific user information across directory services. It also works on both public networks and private intranets. This user-friendly language is one of the easiest ways to access, modify, and authenticate information in virtually any directory.
June 7, 2022
Read More