Using Access Server With JumpCloud
VPN, SaaS, and everything in between: OpenVPN Access Server Combined with JumpCloud's LDAP-as-a-Service Provides Integrated Holistic Access Control. Simplify and Secure Your Team’s Access With This Powerful Combination.
Editor's Note: As of July 2022, OpenVPN Access Server now supports SAML natively.
JumpCloud’s Directory-as-a-Service® is a cloud-based platform enabling IT teams to securely manage user identities and connect them to resources they need regardless of provider, protocol, vendor, or location.
OpenVPN Access Server, built on the most widely-used and respected VPN protocol in the industry, provides powerful solutions to:
- Secure data communications.
- Provide secure remote access for employees and IoT.
- Provide Internet privacy and networking cloud data centers.
Together, they combine powerful security with simple scalability.
Interested in learning how you can manage your IT resources, remote access, and network security with a combo that was built with your DevOps team in mind?
We'll show you how, step by step.
Steps to integrate OpenVPN Access Server with JumpCloud using LDAP-as-a-Service
Before you begin
For these steps, we assume you already have your Access Server set up as well as an account with the Directory-as-a-Service provider, JumpCloud. The following will help you to integrate the two so users can login to OpenVPN with their JumpCloud credentials. Access Server will refer to JumpCloud’s LDAP directory to authenticate users and grant access.
Create and configure a bind user
Begin by creating a user in JumpCloud that will make the handshake and has the authority to scan the LDAP tree. This is called the Bind User.
From your JumpCloud console, create a new user through Manual user entry. Define the following:
- Username (make sure this is a unique name such as LDAP).
- Email (JumpCloud requires each user to have a unique email).
- Click on Specify initial password, rather than sending a welcome email and define the Bind User’s password.
- Click on Enable as LDAP Bind DN (click OK if you receive a pop up that your user must also be enabled in the JumpCloud LDAP directory).
- Save your user.
Once you’ve created your Bind User, click on it to open the details. Under LDAP Distinguished Name, you’ll copy that information over to Access Server in the steps below.
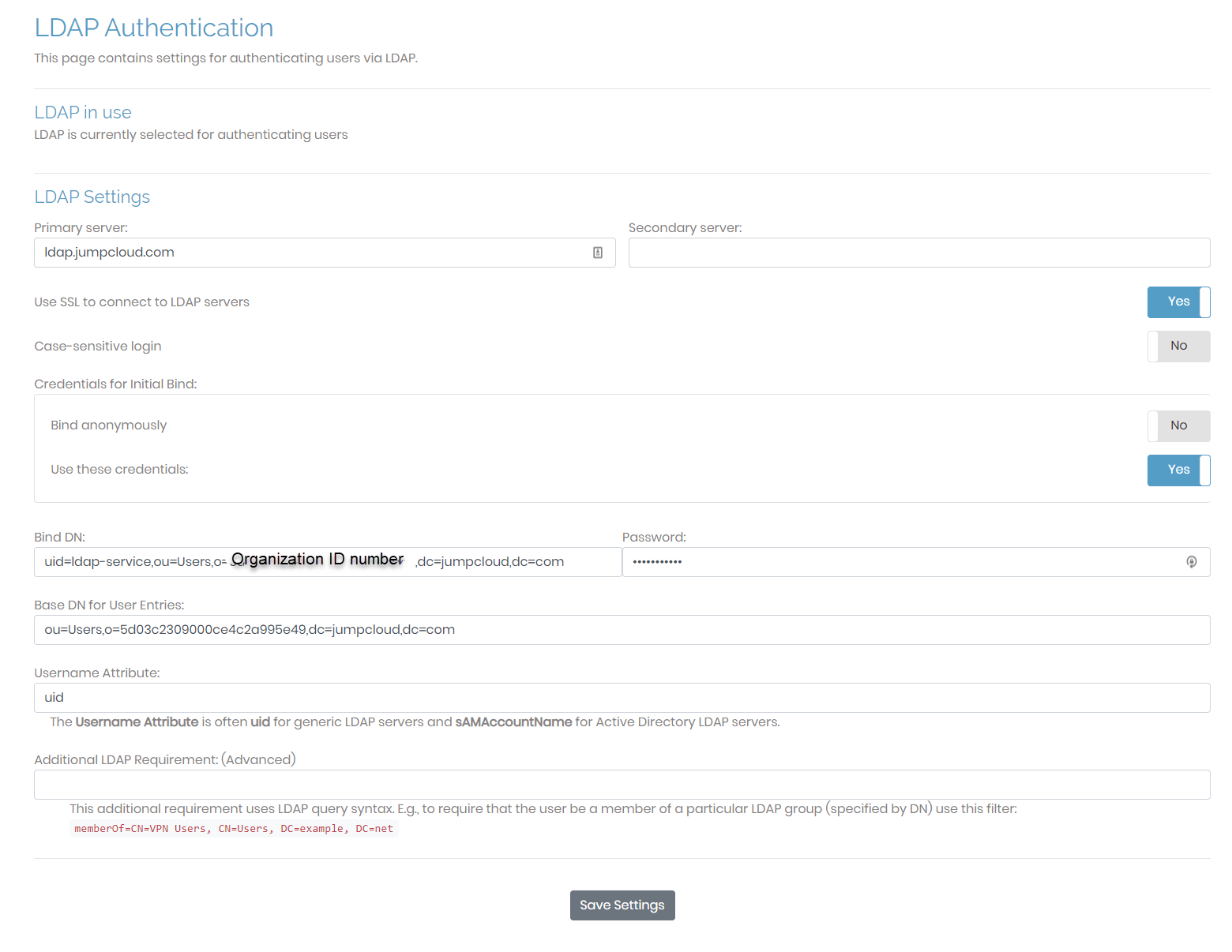
Set up OpenVPN Access Server for LDAP
Navigate to your OpenVPN Access Server Admin Web UI and login as an administrator. Follow these steps to define the LDAP configuration:
- Click Authentication > LDAP.
- Fill out the settings for these fields:
Primary server ldap.jumpcloud.com Use SSL to connect to LDAP servers ‘Yes’ Credential for Initial Bind ‘Yes’ for Use these credentials Bind DN Copy and paste the LDAP Distinguished Name LDAP query from your JumpCloud Bind User. Example:
uid=LDAP,ou=Users,o=[ORGANIZATION_ID],dc=jumpcloud,dc=comPassword Enter the password you defined for your Bind User Base DN for User Entries Copy and paste the LDAP query from your bind user, starting with “ou=Users”. Example:
ou=Users,o=[ORGANIZATION_ID],dc=jumpcloud,dc=comUsername Attribute uid - Click Save Settings.
- If you do not currently have authentication set to LDAP, click Use LDAP at the top of the page or under Authentication > General.
- Click Update Running Server.
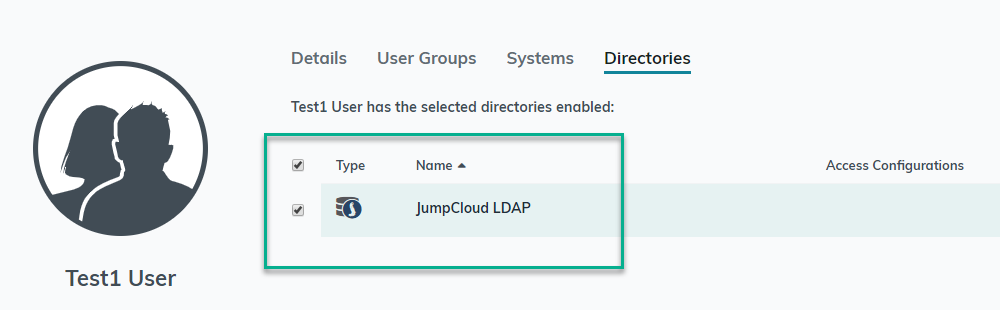
Assign JumpCloud Users to LDAP Directory
For Access Server to find your JumpCloud users, they must be enabled in the JumpCloud LDAP directory. If they are not, you can do so by clicking on Directories/LDAP, clicking on JumpCloud LDAP and selecting them under the Users tab. You can also do this one user at a time from the Users section.
Now that your users are enabled in the LDAP directory and you have set up your Access Server to authenticate over LDAP, they can login to your VPN using their JumpCloud credentials.
Troubleshooting
We provide detailed troubleshooting guides on our site:
- For specific LDAP tips, refer to LDAP Troubleshooting Guide for OpenVPN Access Server.
- For general authentication problems and command line tools, refer to Troubleshooting Authentication Problems.
Here are a few specific areas you may find with your JumpCloud setup:
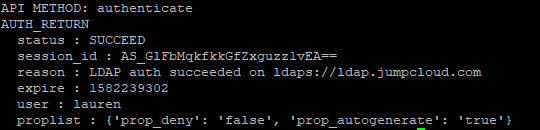
If a user can’t login, use the authcli tool to see what’s happening
- With root access on your Access Server machine, change directory to /usr/local/openvpn_as/scripts/
- Use this format for the tool:
./authcli --user [USERNAME] --pass [PASSWORD] - Here’s a sample output of a successful authentication attempt with JumpCloud:
If you get the error user not found from authcli
- It’s likely that you need to enable your user in the JumpCloud LDAP Directory. Refer to “Assign JumpCloud Users to LDAP Directory” above.
OpenVPN & Jumpcloud co-hosted a FREE webinar.
We recorded the great tutorial so you could watch it for free. Here’s what it covers:
- Managing access between employees and contractors – so each user is only granted the resources they actually need
- Simplify logins for your team – with ONE password for everything from VPN to SaaS
- Make sure your data stays powerfully secure as your team grows
MEET OUR WEBINAR CO-HOSTS Meet Our Webinar Co-Hosts

Johan Draaisma
Access Server Product Manager, OpenVPN
With a background in data centers and network architecture in cloud environments, Johan has spent nearly a decade working for OpenVPN, Inc. to support customers with the complexities of integrating OpenVPN Access Server into their various networking environments. Now, as the project lead for Access Server, he guides the team towards an ever-improving VPN server product.

Greg Keller
Chief Strategy Officer, JumpCloud
Greg Keller is a career product visionary and executive management leader. With over two decades of product management, product marketing, and operations experience ranging from startups to global organizations, Greg excels in successful go-to-market execution.
How Does Ldap-as-a-Service Work With OpenVPN Access Server?
Picture this: a growing web content publishing company provides content for high-traffic websites and portals.
A majority of their employees are freelance and/or remote, so they use OpenVPN Access Server to provide VPN access to their HQ corporate network systems, which run the publishing workflow, timekeeping, and payroll services.
They have plans to expand worldwide and adopt SaaS tools — like Adobe Creative Cloud — to replace some of their legacy systems.
The problem is, as the number of their employees grows, it’s becoming more and more difficult to maintain user accounts in local OpenVPN Access Servers — and complexity will only increase as they add new locations.
So how exactly can this company:
- Centrally store employee information?
- Manage access between employees and contractors?
- Simplify login for their team?
- Make sure their data remains secure as their team grows?
The answer? OpenVPN Access Server combined with JumpCloud’s LDAP-as-a-Service solution.
VPN + LDAP Authentication = Powerful Security
JumpCloud’s LDAP authentication system can be used to enforce secure passwords, add Multi-Factor Authentication, and secure SaaS applications. Combining this identity management with access control through OpenVPN Access Server gives you the simplicity to grant contractors with limited access to services within your corporate network.
JumpCloud and OpenVPN Access Server together means you won't have to sacrifice security for convenience – your team will get ease-of-use, with your network will be built on the strongest protocol in the business.
Plus, JumpCloud's service is a managed solution, so the IT department does not have to install, maintain or grow the LDAP servers or the rest of the directory infrastructure – it’s all built in!
All too often, a company’s network security is either too complicated — or ineffective.
But to truly be effective, it can’t be complicated.
LDAP + VPN combines the best of both worlds
Employees can use the same login info across the board — and security is stronger than ever.
LDAP-As-A-Service maximizes VPN security & simplicity
These two powerful tools combined can simplify – and secure – your network resources.
Do more for your team with LDAP + VPN authentication
Ease of use for your team and powerful resources for IT.
Learn how OpenVPN Access Server can provide ultimate security – with JumpCloud's ease and efficiency.


