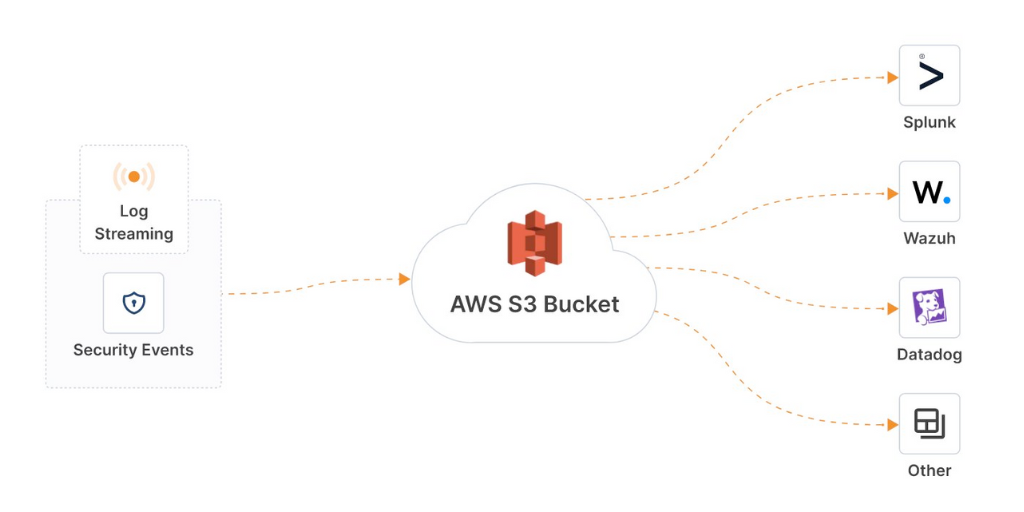
Now Available in Beta — Log Streaming for CloudConnexa®
If your business is keen to ensure IT security and operational tools are up-to-date with crucial events on your CloudConnexa® Wide-Area Private Cloud (WPC) overlay network, one of our recently-released features does just that.
Log Streaming allows your business to holistically monitor the CloudConnexa network and your IT infrastructures. Instead of using the Administration Portal to monitor CloudConnexa, you can pull log events from CloudConnexa into the same IT tools you use to optimize your IT infrastructure, monitor it in real time, set up alerts, reduce costs, and improve customer satisfaction.
January 17, 2024
Read More

OpenVPN Announces SOC 2® Compliance
A recent study found that the epidemic of data breaches more than tripled between 2013 and 2022, exposing over 2.6 billion personal records in the past two years alone. Making sure your SaaS vendors are secure is crucial in protecting your customers' data — which is why OpenVPN continually seeks security validation and testing. Recently, we were awarded our SOC 2 certification, highlighting our commitment to privacy and security. In this post, we share more information about the certification, as well as our ongoing efforts.
January 9, 2024
Read More

Partner Tips: Getting Client Buy-In for ZTNA
When it comes to implementing a zero-trust architecture, getting client buy-in is essential. Here, we offer a few tips and tricks to help your clients embrace ZTNA little by little, while making your job as their MSP easier.
January 9, 2024
Read More

NetworkinGuys Leverages OpenVPN Access Server for Secure and Scalable Client Connectivity
Founded in 2003, NetworkinGuys has carved a unique niche for itself. Here's how they use Access Server for their wide array of clients.
January 8, 2024
Read More

That’s a Wrap! OpenVPN at Gartner IOCS 2023
Earlier this month, the OpenVPN team attended the Gartner IT Infrastructure, Operations & Cloud Strategies Conference. The conference, hosted in Las Vegas, brought leaders from around the globe together to discuss how to get more value, reliability, and agility from technology vendors and investments. If you were unable to attend the conference, we have a […]
December 15, 2023
Read More

Navigating Cybersecurity: Choosing Between All-In-One Platforms and Point Solutions
The cybersecurity industry, and SaaS as a whole, is continually reshaping and changing through acquisitions. These deals have led to a boom in consolidated platforms offering multiple bundled solutions, and more companies attempting to satisfy multiple use cases through a diverse product portfolio. However, these all-in-one platforms come with a cost (literally and figuratively). IT […]
December 15, 2023
Read More
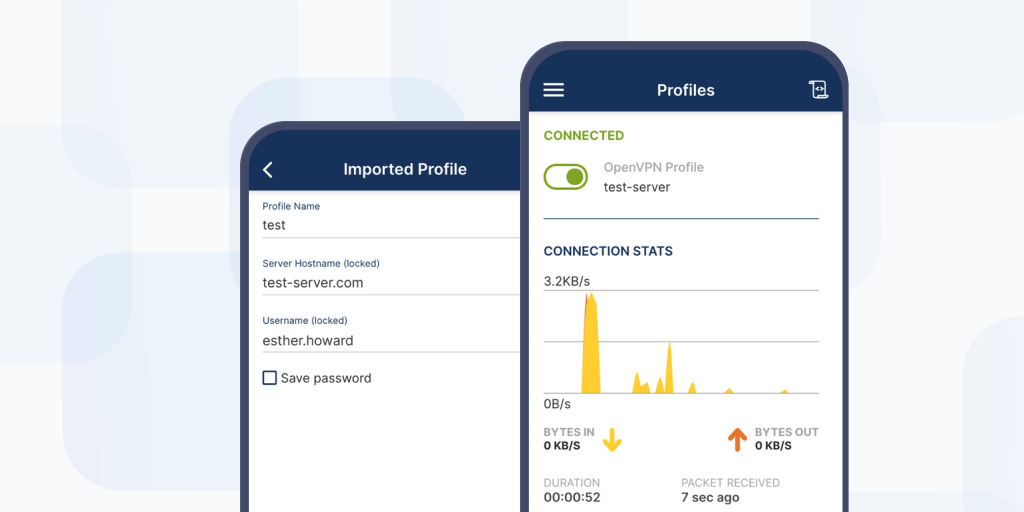
How to Launch the Windows and MacOS OpenVPN Connect Client
Once you’re set up with CloudConnexa, how do you get your team to connect? Here’s a quick how-to for directing each user to get them up and running.
December 4, 2023
Read More

How To Deploy a Connector on CloudConnexa
Are you feeling a little lost when it comes to deploying connectors on CloudConnexa? We've got you covered.
November 22, 2023
Read More

Now Available — Improved and Updated Access Visibility
CloudConnexa is now CloudConnexa® — learn more here. At OpenVPN, we’re continually improving and enhancing our products. Customer feedback is a major part of that process. We recently announced the release of Access Visibility with CloudConnexa® in Beta, and we are happy to announce that Access Visibility is now out of Beta and marked as […]
November 15, 2023
Read More
Trail of Bits Validates Security Strength of OpenVPN
With over 60 million downloads of OpenVPN’s core open source software, 20,000+ business customers, and hundreds of companies who use the OpenVPN protocol in their own products, you may be wondering: Is the OpenVPN protocol safe? It’s a valid question. Recent survey results that found 96% of roughly 1,700 codebases contained open source software and […]
November 15, 2023
Read More

Zero Trust With OpenVPN Protocol for Network Access = Our ZTNA-Capable Solutions
CloudConnexa is now CloudConnexa® — learn more here. What is Zero Trust Network Access (ZTNA)? According to Gartner, "Zero trust network access (ZTNA) is a product or service that creates an identity- and context-based, logical access boundary around an application or set of applications. The applications are hidden from discovery, and access is restricted via a trust […]
October 31, 2023
Read More

Have Extranets Become Extinct?
In today's fast-paced and interconnected business landscape, collaboration between organizations, partners, suppliers, and customers plays a crucial role in driving success. Traditionally, extranets have served as a secure means of facilitating communication and information exchange between two organizations. However, with the rise of modern technologies, the relevance of traditional extranets has been called into question.
In the latest expert blog post from our Product team, we explore the changing landscape of extranets, the emergence of modern collaboration platforms, and how the Cloud Connexa AppHub is revolutionizing the way organizations interact and share access to private applications.
October 23, 2023
Read More

October is Cybersecurity Awareness Month...
October is not just the month of pumpkins and spooky costumes; it's also Cybersecurity Awareness Month, a perfect time to reflect on the downright scary side of cybersecurity risks we all face. In the spirit of Halloween, we're going to explore some truly terrifying cybersecurity statistics that might just send shivers down your spine. But these numbers are more than just spooky stories; they represent real dangers that businesses and individuals face every day.
October 16, 2023
Read More

7 Best Practices to Consider for Site-to-Site Networking
Does your business need to implement a site-to-site networking solution that’s up to today’s cybersecurity demands? We’re here to help. Below are seven solutions, frameworks, and best practices to consider to ensure your setup is configured to offer optimal security.
October 11, 2023
Read More

Now Available — Access Visibility With CloudConnexa®
CloudConnexa is now CloudConnexa® — learn more here. As leaders in virtualized networking, we at OpenVPN understand that you value transparency, traceability, and accountability in your network security solution. That’s why we’ve recently enhanced Cloud Connexa with Access Visibility, a new feature that provides granular insights about traffic flows through a wide-area private cloud (WPC) […]
September 20, 2023
Read More