
Secure Remote Access
Get secure remote access for business through OpenVPN's tailor-made solutions for remote and hybrid teams.
Enforcing Zero Trust
Build the foundation for your Zero Trust strategy with a Zero Trust VPN.
Secure IoT Communications
Mitigate online threats and safeguard your network with robust DNS security protection.
Cyber Threat Protection and Content Filtering
Enforce strong access control and protect sensitive data with OpenVPN's SaaS security solutions.
Protecting Access to SaaS
Protect your company’s network and digitized supply chain with cloud-based security.
Restricted Internet Access
Create a balance between accessibility and security – all without hindering performance.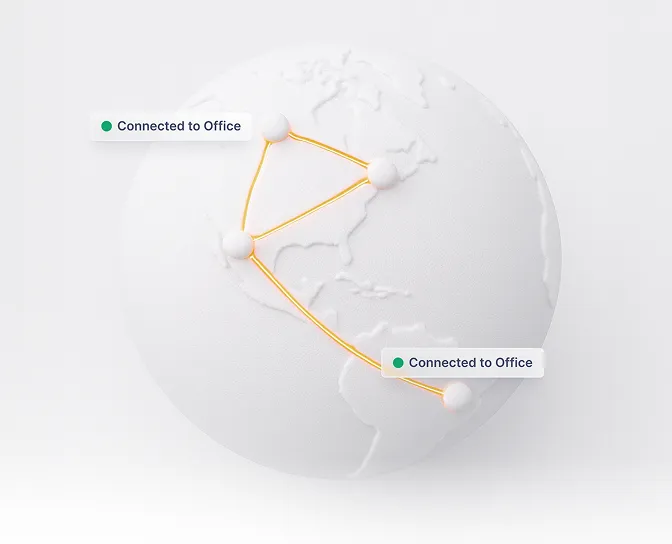
Site-to-Site Networking
Whether at the office, a branch, working remotely, or at headquarters, security connect your networks.
Business VPNs
Connect your remote or hybrid workforce, no matter the size of your business or where they’re located.