HomeAccess Server
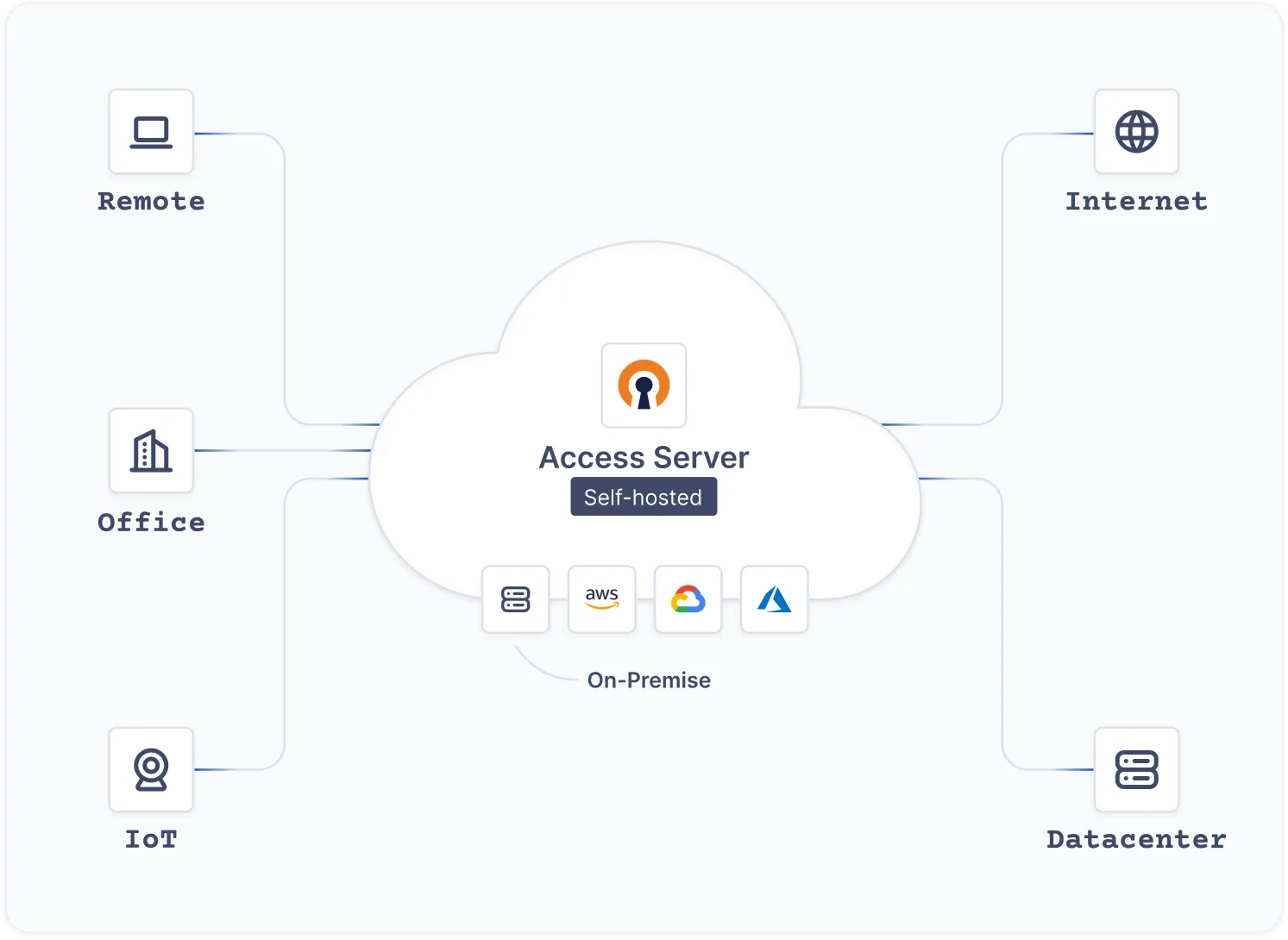
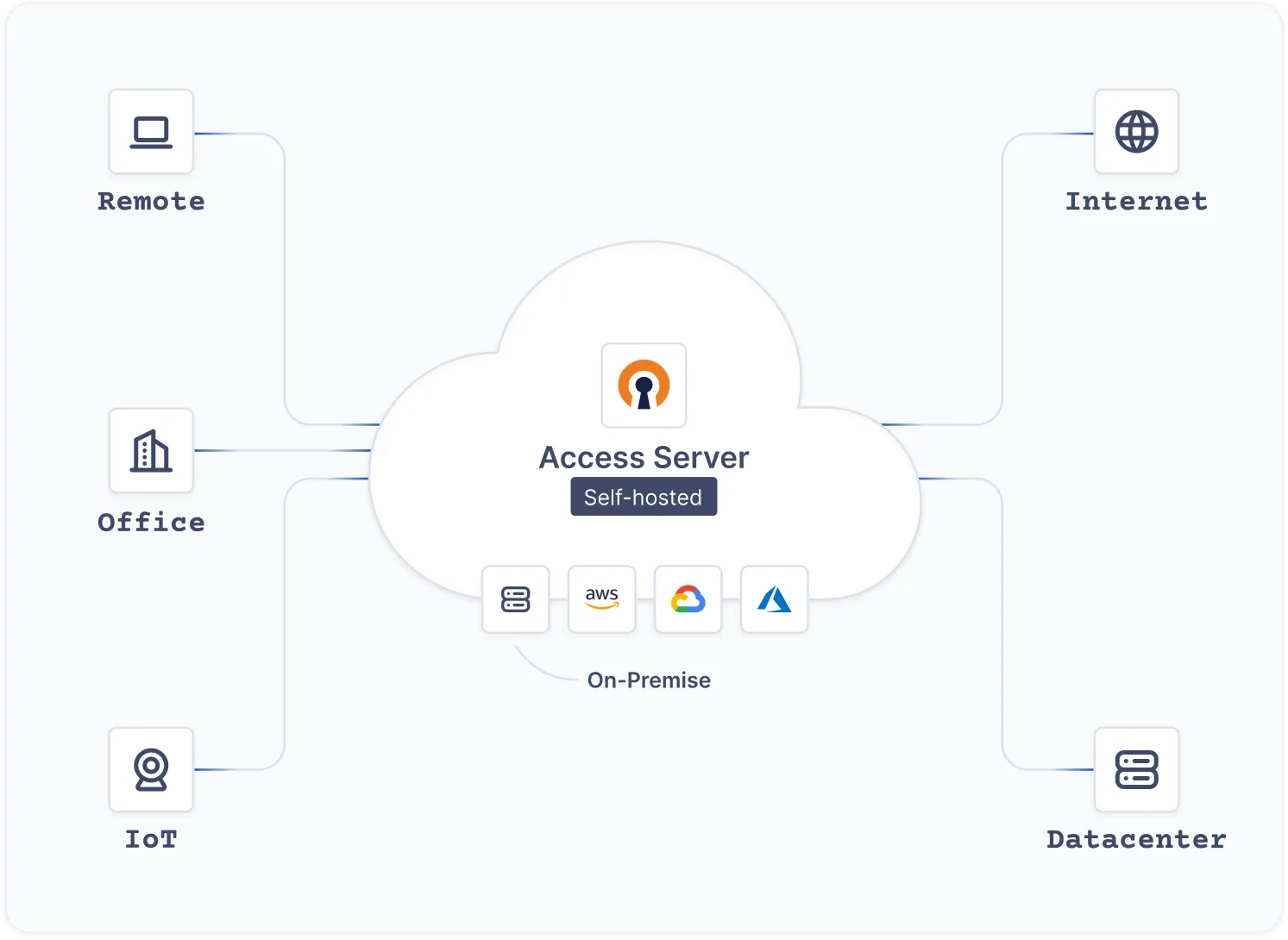
Fast and Easy Zero-Trust VPN Fully in Your Control.
High-speed connections with zero-trust controls, completely hosted in your environment.
4.6 ratingThe #1 Business VPN
Trusted by 20,000+ organizations for over two decades.


High-speed connections with zero-trust controls, completely hosted in your environment.


On Linux OS
On virtual appliances & Containers
On public clouds
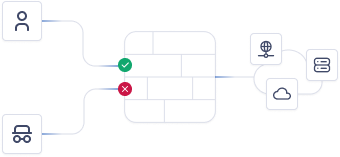 Zero-trust controlsEnhanced security through multi-dimensional verification factors.
Zero-trust controlsEnhanced security through multi-dimensional verification factors.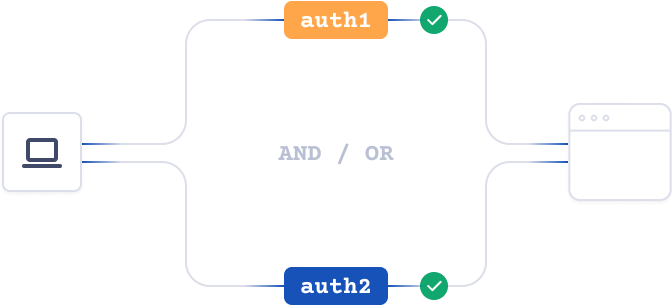 Mix & match authenticationChoose from various methods: PAM, RADIUS, LDAP, SAML, local, or custom.
Mix & match authenticationChoose from various methods: PAM, RADIUS, LDAP, SAML, local, or custom.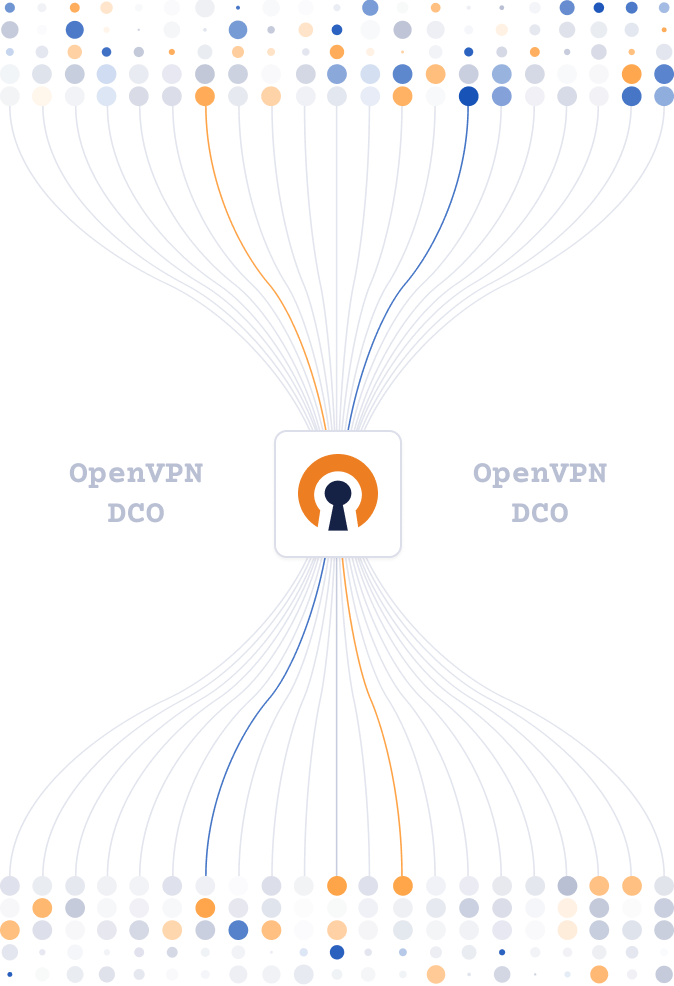

Easy to configure options, add users, and that it has two factor authentication built in. You can configure the system to allow connections on common ports so that you're able to connect from pretty much anywhere in the world.
Configuring and updating my own server is super simple. In my experience, I've always had some difficulty setting up hardware VPN appliances, but OpenVPN was no-nonsense.
The OpenVPN Access Server AMI is a great out of the box VPN solution for your AWS VPC...
OpenVPN offers users a very simple and secure VPN option that is both economical and quick to install. Users are able to easily install it on their client devices.
The availability of client software for all operating systems and mobile devices means my customers can connect regardless of their setup.
Excellent, flexible solution for our Azure environment.
 SOC 2 Type 2 Compliant
SOC 2 Type 2 Compliant HIPAA Compliant
HIPAA Compliant GDPR Compliant
GDPR Compliant ReportsApr 26, 2025
ReportsApr 26, 2025Complimentary Gartner Report: Emerging Tech: Universal ZTNA Drives Secure Access Consolidation
Read More