Clicking the Wrong Link Shouldn’t Be Game Over
Deploy DNS security services, internet policies, and content enforcement for cyber threat protection effortlessly.

Deploy DNS security services, internet policies, and content enforcement for cyber threat protection effortlessly.


Cyber Shield, a built-in feature of CloudConnexa, delivers DNS-based content filtering so organizations can avoid malware infections and excessive bandwidth use by controlling employee access to potentially harmful external websites.
Learn More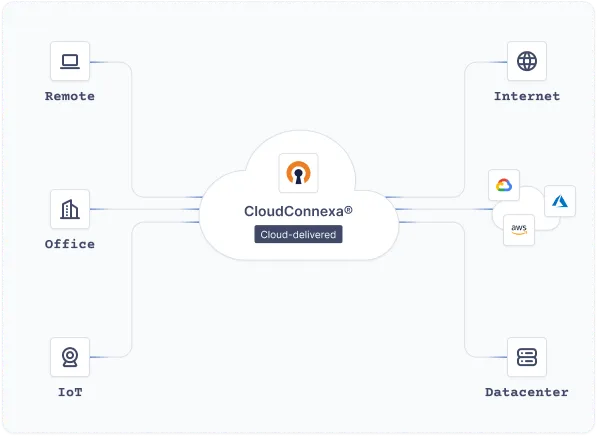
Easy to configure options, add users, and that it has two factor authentication built in. You can configure the system to allow connections on common ports so that you're able to connect from pretty much anywhere in the world.
Configuring and updating my own server is super simple. In my experience, I've always had some difficulty setting up hardware VPN appliances, but OpenVPN was no-nonsense.
The OpenVPN Access Server AMI is a great out of the box VPN solution for your AWS VPC...
OpenVPN offers users a very simple and secure VPN option that is both economical and quick to install. Users are able to easily install it on their client devices.
The availability of client software for all operating systems and mobile devices means my customers can connect regardless of their setup.
Excellent, flexible solution for our Azure environment.