Plugins Using Access Server's Post-Authentication Programming Hook
Abstract
What is a post-auth script, and how does it apply to Access Server? Find your answers and examples here.
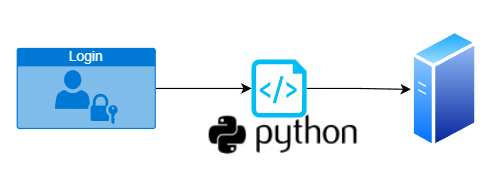
You can extend Access Server's built-in authentication methods using a post-authentication Python3 script to add additional user connection requirements, such as MFA or other custom checks. You can also use a post-auth script to implement your own custom authentication method. These post-auth script implementations are Access Server plugins.
This topic provides information about the different post-auth options and various post-auth scripts you can download from our site and customize for your system.
What is a post-auth script?
Post-auth means post-authentication. It uses a custom Python3 script loaded into Access Server to add additional checks and challenges, such as hardware address checking or custom multi-factor authentication.
Post-auth script tutorials
In addition to the specific post-auth scripts below, use these tutorials to work with this feature:
Working with post-auth scripts
This guide covers writing and using Python scripts for post-authentication in Access Server. It explains key parameters, how to modify the authentication process, and examples for handling user authentication, group assignment, and user properties. It also includes testing guidance.
Important
OpenVPN Inc. provides examples of post-auth scripts, but we don't offer custom ones. Use the example scripts and documentation provided to develop or modify the post-auth script using the Python3 programming language.
Post-auth scripts available
You can follow the tutorials below to implement one of the various post-auth scripts available to customize authentication.
Table 1. Post-auth script tutorials
Hardware Address Registration | Tutorial: How to set up Hardware Address Checking with a Post-auth Script Access Server requests a MAC address or UUID from the OpenVPN client to authenticate with hardware addresses after username and password. The script supports automatic address registration by default. It can also run in manual mode, in which you must manually add approved hardware addresses on the server for users and their devices.
|
PAS-only custom authentication script | Tutorial: Create a Custom Authentication System with a Python Script Using a properly configured post-auth script, you can implement an entirely new custom authentication method in Access Server. The script indicates that it doesn’t need the Access Server to handle authentication by setting the AUTH_NULL parameter to true and must then manage authentication in the script. You then set this authentication method for specific users or groups or as the default authentication method. You can use the custom authentication method against any credential or authentication backend that Access Server doesn’t support out of the box.
|
LDAP group mapping script | Tutorial: How to Set Up LDAP Group Mapping with a Post-auth Script You can assign users to Access Server groups so they inherit specific access rules and settings, a task you can automate using our LDAP group mapping script. Suppose you assign users in your LDAP directory server to groups using the group membership property memberOf. In that case, you can use the memberOf property in a post-auth script when a user signs in to Access Server. Based on rules you must define in the post-auth script, you can automatically have users in specified LDAP groups assigned to specified Access Server groups when they authenticate.
|
RADIUS group mapping script | Tutorial: How to Set Up RADIUS Group Mapping with a Post-auth Script You can assign users to Access Server groups so they inherit specific access rules and settings, a task you can automate with the RADIUS group mapping script. You can also include other settings in the script based on particular RADIUS properties. Users in a RADIUS server can be part of groups with specific properties set. The post-auth script reads and uses these properties to automatically apply group membership and other settings. The post-auth script is primarily designed for Windows Server and mapping users to Access Server groups but may also work on other RADIUS solutions.
|
SAML group mapping script | Tutorial: How to Set Up SAML Group Mapping with a Post-auth Script You can assign users to Access Server groups with specific access rules and other settings inherited from the group, a task you can automate with our SAML group mapping script. Users in the SAML IdP can be part of groups. You must configure this property on the SAML IdP; we provide tutorials for configuring SAML, and this property is usually the group property you can use in the post-auth script when a user logs in at the Access Server. Based on the rules you define in the post-auth script, you can automatically assign users in specified SAML groups to specified Access Server groups when they log in at the Access Server.
|
Duo 2FA | Tutorial: Add Duo Two-Factor Authentication to Access Server You can integrate Access Server with Duo and add two-factor authentication options such as SMS, push notifications, Yubikey, etc. If you use PAM, RADIUS, LDAP, or local authentication, you can use the provided post-auth script to integrate Duo Security into Access Server. To set this up, you download the Duo Security post-auth script for OpenVPN Access Server from GitHub, add an API key obtained from Duo Security into the script in the appropriate section, and load the script into the Access Server.
ImportantIf you use SAML authentication, you must integrate Duo Security into your SAML solution rather than using the custom script. |
iVALT 2FA | Tutorial: Add iVALT Two-Factor Authentication to Access Server You can integrate Access Server with iVALT to add biometric 2FA. The iVALT post-auth script uses facial verification, geofencing, and time zone validation to enhance login security. Download the iVALT script from GitHub, add your secret key, and load it into Access Server.
ImportantDon't enable TOTP MFA when using iVALT, as it causes authentication conflicts. |
Restrict by IP address | Tutorial: Restrict by IP Address with the Post-auth IP Restrict Script You can create a post-auth script restricting users based on their IP addresses. The sample script automatically registers an IP address for a user when they first authenticate and restricts their access to the registered IP address. Users are denied access if they sign in from a new IP address.
|
LastPass 2FA | OpenVPN Access Server VPN configuration for LastPass Universal Proxy |
Host-checker query | Tutorial: Setting Up a Host-Checker Query File on Access Server You can set up a host-checker query file in Access Server to check for specific applications on client devices and report their version numbers. This feature enhances security and compliance by ensuring users meet certain software requirements before connecting to the VPN. You can incorporate these checks into a post-auth script to allow or deny connections based on the results.
|
Challenge/response authentication | Tutorial: Implementing a Challenge/Response Authentication in Access Server Create a custom static or dynamic challenge/response authentication method. (This is different from the built-in MFA TOTP functionality.) Use dynamic challenge/response for flexible, per-session challenges or static challenge/response when you need consistent, predefined challenges embedded in the connection profiles.
|
X.509 attribute-based enforcement | Tutorial: Implementing a Post-Auth Script with X.509 Attributes Use X.509 certificate attributes in a post-authentication script to enforce access policies. Read certificate fields, including subject attributes, extensions, and custom values. Allow or deny VPN connections based on certificate content. Dynamically assign users to groups or apply specific access rules. Implement advanced policy decisions based on certificate metadata.
|
External public key infrastructure
Access Server's external public key infrastructure (PKI) is a plugin option separate from the post-auth function. This feature allows you to integrate Access Server with third-party tools for X509 PKI management instead of using the built-in certificate management capabilities.