TLS Control Channel Security in Access Server | OpenVPN
This topic details how TLS control channel security works in OpenVPN's Access Server.
This topic details how TLS control channel security works in Access Server, how to change the TLS control channel security used by the server and clients, and the impact of making these changes.
TLS control channel overview
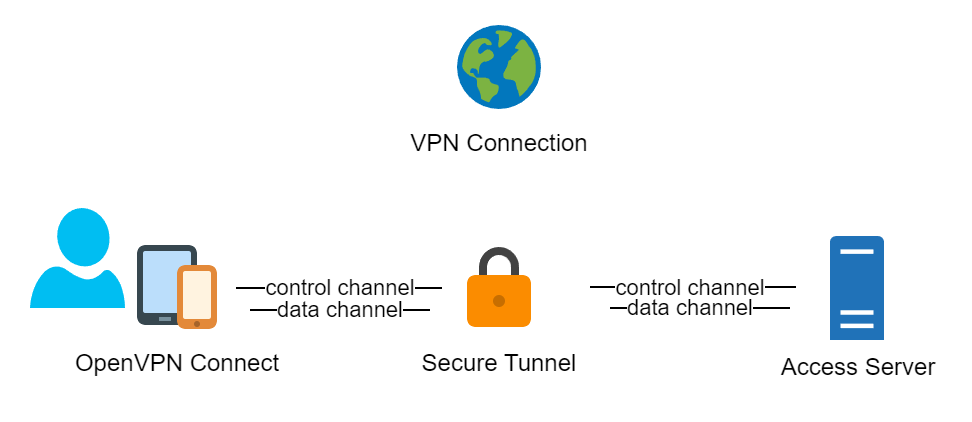
The OpenVPN protocol uses two communication channels during a VPN session:
The control channel: handles authentication, key negotiation, and configuration.
The data channel: encrypts and transports packets.
Access Server 2.9 and newer uses TLS Auth, TLS Crypt, or TLS Crypt v2 to secure the control channel. For a new installation using Access Server 2.9 and newer, TLS Crypt is used by default. While it may be preferable to use TLS Crypt v2 for security reasons, TLS Crypt is the default for compatibility reasons.
Caution
We don’t recommend disabling TLS control channel security, but if you need to do this for certain devices, note that it is not a user-specific setting. The signing and verification of packets work as a filter, similar to a software firewall, so unsigned packets that don’t pass the verification filter are dropped very early during packet processing.
TLS Auth
TLS Auth secures the control channel by signing and verifying the packets with a shared group key. If the pre-shared keys are kept secret, it provides protection against TLS-level attacks with post-quantum resistance.
TLS Crypt
TLS Crypt improves upon TLS Auth by adding symmetric encryption to the control channel. This extra layer of encryption applies even to the key exchange before the TLS session starts. Like TLS Auth, it also provides protection against TLS-level attacks with post-quantum resistance if the pre-shared keys are kept secret.
TLS Crypt v2
TLS Crypt v2 improves on TLS Crypt by using a unique key per connection profile.
Access Server 2.9 and newer can generate and accept TLS Crypt v2 connection profiles even if the TLS control channel security level is set to TLS Auth or TLS Crypt. OpenVPN Connect v3.2 and newer can use TLS Crypt v2, and the installers that Access Server provides for macOS and Windows contain TLS Crypt v2 profiles. OpenVPN Connect v3.3 and newer obtains TLS Crypt v2 profiles by default when importing a profile with the import from URL function in the app. For compatibility reasons, the default profile downloaded from the Client Web UI adheres to the TLS control channel security setting configured in Access Server because not all OpenVPN client versions support TLS Crypt v2.
Access Server 2.8 and previous versions use TLS Auth by default. When you upgrade to Access Server version 2.9, it continues to accept connection profiles with TLS Auth for backward compatibility and generates new connection profiles, when possible, with TLS Crypt v2. This allows a graceful migration of an existing setup with older connection profiles to a more secure setup.
It is possible to run Access Server without additional control channel security. An example is connecting devices that don’t support TLS Auth or when it doesn’t provide added security, such as using a server-locked profile with a publicly distributed group key.
Changing the TLS control channel security setting
You can configure the TLS control channel security in the Admin Web UI or the command line.
Changing the TLS control channel security settings for new Access Server installations won't likely impact existing VPN clients. For existing installations with many installed and configured VPN clients, changing the TLS control channel security setting without updating the connection profiles on the client devices may result in connection failures. Whether or not connection failures occur depends on the type of connection profiles used by the VPN clients. After changing the setting, VPN clients that can’t connect must get a new connection profile and/or update the VPN client software to a version that supports the TLS control channel security level.
Compatibility of control channel security configured on Access Server with listed OpenVPN client programs
Client program used | Setting configured on Access Server | |||
|---|---|---|---|---|
None | TLS Auth | TLS Crypt | TLS Crypt v2 | |
Connect v3.2+ | √ | √ | √ | √ |
Connect v3 previous versions | √ | √ | √ | x |
Connect v2.7.111+ | √ | √ | √ | √ |
Connect v2 previous versions | √ | √ | x | x |
Open source v2.5+ | √ | √ | √ | √ |
Open source v2.4 | √ | √ | √ | x |
Open source v2 previous versions | √ | √ | x | x |
Important
OpenVPN Connect v3.2 can use TLS Crypt v2 type connection profiles, but importing a profile from a URL from an Access Server that isn’t configured for TLS Crypt v2 control channel security results in an imported profile with that specific setting. OpenVPN Connect v3.3 and newer retrieves a TLS Crypt v2 connection profile if the server is Access Server 2.9 or newer when the import from URL function is used.
Compatibility of control channel security setting configured on Access Server with listed connection profile types
Client profile | Setting configured on OpenVPN Access Server | |||
|---|---|---|---|---|
none | TLS Auth | TLS Crypt | TLS Crypt v2 | |
Any profile of type 'none' | √ | x | x | x |
Any profile of type 'tls-auth' | x | √ | x | x |
Any profile of type 'tls-crypt' | x | x | √ | x |
Any profile of type 'tls-cryptv2' | x | √ | √ | √ |
Server-locked from AS 2.8 or previous | √ | √ | √ | √ |
Important
Server-locked profiles from Access Server 2.8 or older use the web service to retrieve a user-locked type profile from the server whenever that type of connection starts. Therefore, this type of connection profile can establish connections no matter the control channel security configuration setting. Newer, server-locked profiles from Access Server 2.9 work differently. They do not communicate through the web service but function as any other type of connection profile. An advantage of the newer server-locked connection profiles is that they can function with any client, not just OpenVPN Connect.