Remote Desktop: Flexibility and Productivity
Picture this: it’s a Wednesday morning in the dead of winter. Snow is piled up so high you can barely see the top of your car. The plows are nowhere to be seen; you can’t even get ten feet down the street without your car getting stuck.
There's no way you’re making it to the office.
Fortunately you have your laptop (or other mobile device), so you can still get work done.
But there’s an issue: your laptop has less computing power than your office computer. That makes completing your usual tasks extremely difficult. Maybe impossible.
What do you do? You can turn on remote desktop access and connect to your work computer as if you were right there at your desk. If you have an internet connection, and the remote computer is turned on and set up for a remote desktop connection (RDC), you can use a remote desktop session to access files and applications.
What is a remote desktop?
Remote desktop software (or an operating system with a remote desktop feature) allows a computer's desktop to run remotely on one system while displaying on a separate device. Whereas a VPN provides network access, a remote desktop allows you to access a totally separate system/device. When you enable remote desktop access you can access a particular device from anywhere in the world.
Remote access turns your mobile device into a figurative window that lets you see what you do on your work computer. You can access your workstation programs and files, and have the computing power you need.
With a remote desktop, bad weather won't keep you away from the office. You and your employees can access your computer and applications from anywhere.
But how do you provide remote desktop access? More importantly, how do you secure Windows Remote Desktop Services (RDS), and make sure you're in control of who accesses the desktops?
Note: Windows Remote Desktop Protocol (RDP) clients are available for Windows, Android, iOS, and macOS operating systems.
Pros And Cons of Remote Desktop Access
Pros:
Several benefits make remote desktops an excellent choice for businesses of all sizes:
Productivity — Remote desktop lets employees access the computing power, apps, and resources they need, anywhere. This boosts productivity.
Savings — Remote desktops mean you can adopt a BYOD (Bring Your Own Device) policy for remote workers. BYOD translates to hardware savings.
Access — Remote desktops allow you to access your desktop data from anywhere in the world, which means you don’t have to be as dependent on flash drives. It’s still a good idea to back-up information — especially before heading out on a big work trip — but a remote desktop means that even if you forget your flash drive, you can still get the job done.
Cons:
In most case remote desktop access is only protected by a password. Remote employees using unsecured public WiFi targets for hackers looking for usernames and passwords. Employee password sharing can help bad actors gain access, too. Once they're in, they can do even more damage.
In order to fully secure a remote desktop, a VPN is the best option. With a VPN like Access Server, you have secure access to the network, and then the VPN server has least a privilege access policy setup that would limit an employee to using a remote desktop to connect only to his or her computer's IP address. Employees wouldn’t be able to tap into their cubicle-mates desktop, and hackers won’t be able to get their hands on your sensitive business data.
Remote Desktop Connection Over a VPN
Let's use an educational software company as an example. The company develops learning software that it sells to public libraries and schools. It also offers direct sales online.
The company's software works with Windows. They use Windows Networking and Windows Domains, as well as Windows Active Directory.
The company wants employees to be able to work anywhere in the world, with access to the tools they'd have on-site.
The company opts to give employees Microsoft remote desktop access. This lets them access office workstations from anywhere. They use OpenVPN Access Server for reliable security and VPN access to the office network.
Access Server is installed on the company network. LDAP, and Windows Active Directory, ensure users are who they claim to be. Using Active Directory allows employees to use the same credentials for remote access and the VPN.
Group access controls corresponding to the Active Directory Groups is set up in the Access Server. This gives remote desktop users access to the same services they would have at the office.
Now employees can connect to the company’s private network. A secure VPN connection is created with Windows user account credentials.
How To Use Remote Desktop Securely
You can use the Microsoft Remote Desktop app to connect to a remote PC or virtual apps and desktops. This app helps you be productive no matter where you are.
Then Access Server can be set to authenticate users against Windows Active Directory which will give you greater access control, and allow the user to use the same Windows credential to authenticate with VPN.
Step by step instructions with pictures can be found here: How to authenticate users with Active Directory
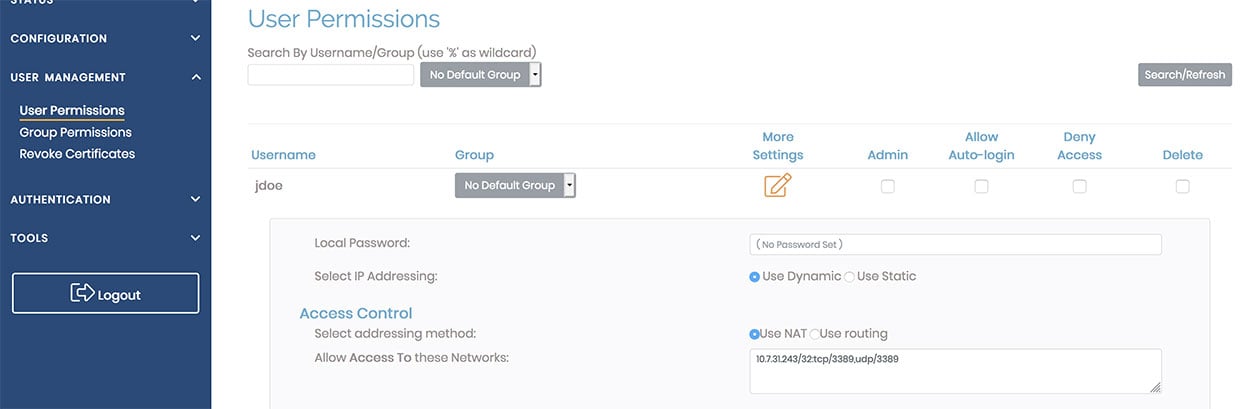
A remote desktop protocol can use port 3389 on either TCP or UDP. As seen in the above image, the user has been given explicit access to the remote desktop server running on the work computer at IP address 10.7.31.243.
Using OpenVPN Access Server provides additional security in several different ways:
- Only devices with the correct client certificate can connect
- Google Authenticator can be used for Multi-factor authentication of user identity
- On a VPN connection, least-privilege access can be enforced by only allowing RDP access to specific workstations.
Remote and hybrid work is more common than ever. That means securing remote desktop connections is more important than ever. Visit the OpenVPN Secure Remote Access use case page.